What Internal Compliance Really Means (And Why You Can’t Leave It to HR Alone)

Internal compliance is a shared responsibility across all teams, not just HR, requiring clear ownership of different compliance domains and ongoing processes rather than one-time policy creation. Building compliance into daily operations through assigned responsibilities, automation, and regular reviews creates trust, scalability, and resilience while preventing dangerous blind spots that emerge when compliance is siloed in a single department.
Internal compliance isn't just a set of policies. It's a shared responsibility across your company. Leaving it all to HR creates blind spots. Building it into your operations builds trust, scalability, and resilience.
It's Not Just HR. And It's Not Just Legal.
This article builds on our previous guide on hidden compliance risks—now we dig deeper into how internal compliance actually works and who should own it inside your company.
Many growing companies treat internal compliance like a checklist: write a few policies, store some documents, and have HR send reminders. But internal compliance is more than that—it's the connective tissue between your processes, people, and values. It ensures that what you say you do on paper is what actually happens in practice.
If you rely on HR alone to manage it, you're likely missing major risk areas that sit outside their domain.
So What Is Internal Compliance?
Internal compliance refers to your company's ability to design, implement, and uphold its own standards—legal, ethical, procedural, and cultural. It's not just about following the law; it's about aligning your team with how your business operates and what it stands for.
A well-functioning internal compliance system typically includes documented internal policies and processes, employee training and acknowledgment, controls over system access, documentation of incidents and approvals, internal audits, and feedback loops to evolve these systems over time.
In short: Compliance isn't just about avoiding penalties. It's about making sure the right things happen, the right way, every time.
Why HR Can't Own Compliance Alone
HR plays a vital role in compliance, especially around employee experience and policies. They're typically responsible for distributing policies during onboarding, running employee training sessions, managing behavioral incidents, and collecting policy acknowledgments.
However, critical parts of compliance extend far beyond HR's reach:
- Revoking access credentials in company systems falls under IT and security teams.
- Managing NDA expirations and contract obligations is usually handled by Operations or Legal.
- Designing a system for data retention or preparing for an audit involves Finance and senior leadership.
If compliance lives in HR alone, it becomes a silo. And silos leak.
Ready to Streamline Your Compliance?
Discover how Humadroid can simplify your compliance management process.
Who Actually Owns Internal Compliance?
Every team touches compliance in some way. But someone has to lead. Here's a functional breakdown:
Note: If your company doesn't yet have a dedicated role for any of these areas (e.g. no IT lead, no legal advisor), the responsibility often defaults to the CEO or Operations. Clarity is more important than coverage—someone needs to own each domain.
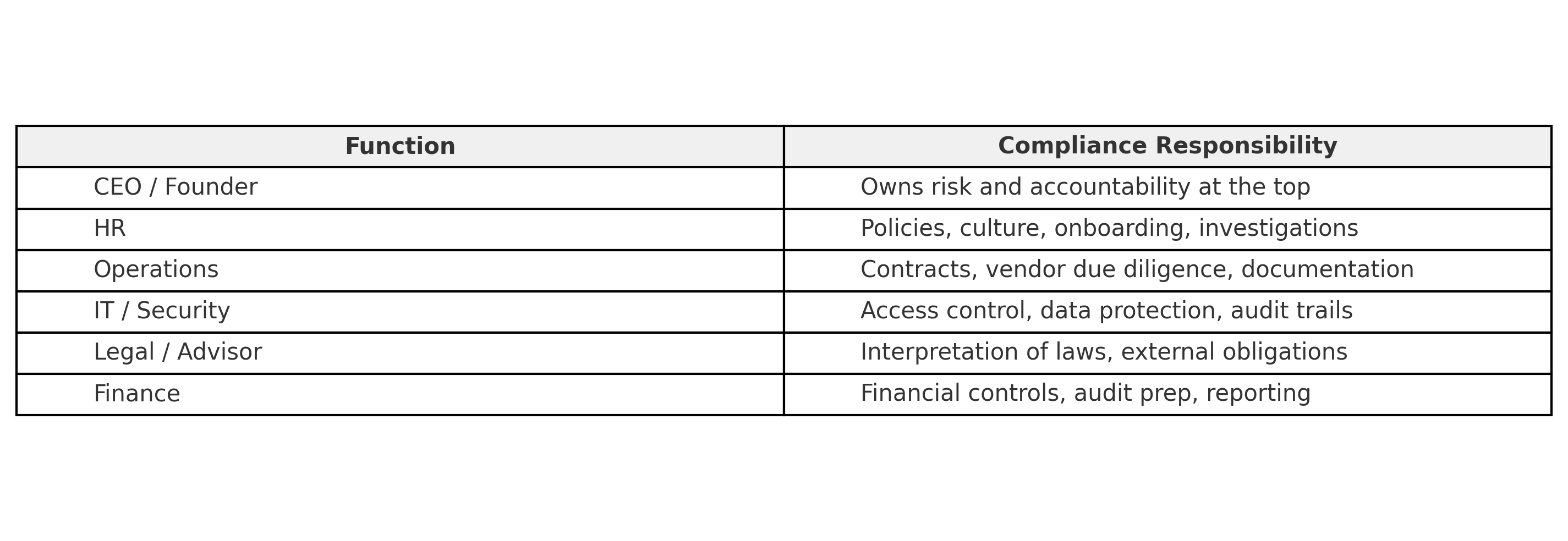
In small teams, these may overlap. But the key is clarity: everyone should know their role in maintaining compliance.
Compliance Is a Process, Not a Project
Treating compliance like a one-off task, "let's just get the policies done", is a classic mistake. Internal compliance is a living, cyclical process that requires regular upkeep and review.
It starts with defining your standard and policies. Then you implement them across teams and tools. Next, you monitor behavior, system access, and compliance events. Finally, you improve based on audits, incidents, and evolving needs. Internal Compliance processes implemented well in the early stage of business will help you in the future without a doubt.
Use a quarterly rhythm. Compliance should evolve with your business.
How to Build an Internal Compliance Mindset
Even without a legal department, you can build compliance into daily operations. Assign clear responsibilities for policy ownership, access control, and documentation. Automate what you can—acknowledgments, storage, access tracking. Regularly review tools and vendors to ensure compliance alignment. Centralize internal documentation, and above all, empower employees to speak up.
And when a security breach does happen, because eventually, it might, your team should know exactly what to do. That includes:
- Notifying the appropriate internal contact or team immediately
- Documenting what happened and when
- Identifying which data or systems may have been affected
- Triggering your incident response or breach notification process
- Communicating transparently with affected users or partners (if required by regulation)
Having a plan before a breach gives your company the best chance to mitigate impact and maintain trust.
Platforms like Humadroid help simplify this process, even for small and fast-growing teams.
Frequently asked questions
Do we really need formal policies if we're only 10 people? +
Yes. Policies aren't about company size—they're about demonstrating that you've thought through how you handle data, security, and operations. A 10-person startup seeking enterprise clients will face the same compliance questions as a 100-person company. Documented policies show maturity and reduce individual liability.
Can we handle compliance entirely in-house without consultants? +
Many startups do, especially with modern automation tools. The key is having someone own the process, using frameworks like SOC 2 or ISO 27001 as guides, and maintaining consistent documentation. Compliance automation platforms provide the structure and guidance that previously required consultant expertise.
Who should be responsible for internal compliance in a small business? +
Internal compliance should be a shared responsibility across teams, not just HR alone. While HR handles employee policies and training, IT manages system access, Operations handles contracts, and Finance oversees audit preparation. Humadroid's AI can help coordinate these responsibilities by providing 24/7 guidance to all team members at a fraction of the cost of hiring dedicated compliance staff.
How does AI help automate internal compliance management for SMBs? +
AI-powered platforms like Humadroid can automate policy distribution, track employee acknowledgments, monitor system access, and centralize compliance documentation across all departments. This eliminates the silos that occur when compliance is managed manually by HR alone, providing 24/7 compliance assistance for $125-250/month instead of hiring $200k+ consultants.
What's the biggest mistake companies make with internal compliance? +
The biggest mistake is treating internal compliance as HR's sole responsibility and as a one-time project rather than an ongoing process. This creates dangerous blind spots in areas like IT security, contract management, and financial controls. Humadroid's AI helps avoid this by providing comprehensive compliance guidance across all business functions, ensuring nothing falls through the cracks.


